Data Breach
Email Security: Solving the Main Cause of Data Breaches
Email is an indispensable tool in office collaboration and communication. That’s true even in the era of information overload, in which users’ inboxes are flooded with messages. But malicious actors…
Law firm cybersecurity: does your firm measure up?
At Integris, law firms were our first clients. Today, we’re incredibly proud to say we’re providing managed IT services to more than 100 law firms across the US, and the…
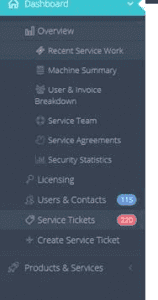
A client portal is an MSP’s ‘litmus test’ for client-centricity
Key takeaways: Why does a client portal signal high-quality MSP service? Organizations that are considering IT managed service provider support want the highest level of service, and they want access…
The National Public Data Breach of 2024: How to Shield Your Data from Dark Web Hackers
Every day, there’s another screaming headline about “the biggest data breach in history.” This time, however, it really may be “the big one.” In August 2024, a dark web hacker…